Recovery Brute Force Attacks
I've read this TechNet blog post, but I still can't determine how secure BitLocker is against a malicious user that attempts to brute force attack the recovery password. Is anyone familiar with this? Also, how about offline brute force attacks against the recovery password?
.Think your password is secure enough?You may want to think again. In 2014, nearly half of Americans had their personal info exposed by hackers – and that doesn’t even count the many companies that experienced breaches.And with more and more businesses storing their information in the cloud and using SaaS solutions like and, keeping your information safe becomes even more important.Selecting an obscure and complex password and changing it frequently can spell the difference between keeping your data secure and having your personal information stolen. We’ve gathered insights and advice to empower you to tighten up your online security – and keep hackers out of your personal business.To get started, we set out to discover just how quickly a seasoned cracker could “brute-force” various types of passwords (systematically check combinations until finding the correct one) based on factors such as length and character types. We also created an interactive feature that lets you estimate how long it would take someone to crack a password now compared with how long it took in the past. If you come up with an idea for a potential password, our tester can tell you just how secure it is.
Just how many days, weeks, or years worth of security an extra letter or symbol make? How does password strength change over time? The answers just might surprise you. How strong is a typical password now – and how strong was it in the 1980s?
Enter a word (not your current password) and drag the slider to select a year to find out how long it would take for someone to crack the term if it were your password. It could take anywhere from infinite time to a millennium to mere fractions of a millisecond.You can turn the “word list” function on or off as you test passwords. This tool works by cycling through a word list containing common words and passwords and then evaluating other factors such as character types. If you enter a password not on the word list, the cracking time will not be affected. But if your password is on the word list, it greatly affects cracking time.Note: The interactive tool is for educational purposes only. Although it does not collect or store your passwords, you should avoid using your current password. How long should your password be?When it comes to passwords, one thing is certain: Size matters.
Adding a single character to a password boosts its security exponentially. In a so-called “dictionary attack,” a password cracker will utilize a word list of common passwords to discern the right one. The list above shows the difference that adding characters can make when it comes to security.For instance, if you have an extremely simple and common password that’s seven characters long (“abcdefg”), a pro could crack it in a fraction of a millisecond. Add just one more character (“abcdefgh”) and that time increases to five hours. Nine-character passwords take five days to break, 10-character words take four months, and 11-character passwords take 10 years. Make it up to 12 characters, and you’re looking at 200 years’ worth of security – not bad for one little letter.
Alpha and numberic charactersCombining numbers and letters rather than sticking with one type of character dramatically enhances password security. A string of nine letters or numbers takes milliseconds to crack. Add a single letter, and your password may become cryptic enough to thwart password crackers for nearly four decades.However, it’s not as simple as swapping your “e” for a “3” or adding a number at the end of a string of letters. Password attacking methods actually take advantage of those common habits. Your best bet is to simply make your password less predictable and more complicated. Asci, lowercase, and numeric charactersCombining several types of characters is an extremely effective way to make your password more cryptic. A simple, common word can be cracked in fractions of a millisecond.
Inject a mix of lowercase and uppercase letters, numbers, and symbols (think @,%, and #), and your password can be secure for more than a decade. Password strength over timeNot every security issue comes down to password character types and length – time is also a major factor. Over the years, passwords weaken dramatically as technologies evolve and hackers become increasingly proficient.
Rdp Brute Attack
For example, a password that would take over three years to crack in 2000 takes just over a year to crack by 2004. Five years later, in 2009, the cracking time drops to four months. By 2016, the same password could be decoded in just over two months. This demonstrates the importance of changing passwords frequently. What if you get hacked?One morning, you open your email, and everything has gone haywire: Friends are chatting you to say they’ve received spam from your address. Your login history looks odd.
You have a pile of bounce-back messages in your inbox and a bunch of strange messages in your sent box. You’ve been hacked – so what should you do?First, recover your email account, and change your password (use our guidelines to formulate a strong one). Complete all the steps, such as changing security questions and setting up phone notifications. Because email is filled with personal information, you should also notify your bank, PayPal, online stores, and any other accounts to discern whether a breach has occurred. Be sure to change other passwords as well. Finally, notify your contacts in case emails sent from your account have compromised their information too. While not getting hacked at all is the best-case scenario, promptly taking these steps can make the best of a bad situation.
Protect yourselfAs time goes on, it only becomes more likely that your password will be hacked – putting your most personal information at risk. By taking a few steps to enhance your password, you can exponentially minimize the risk of a breach. When it comes to passwords, size trumps all else – so choose one that’s at least 16 characters.
And be sure to choose a mix of character types (numbers, uppercase and lowercase letters, and symbols) to further enhance its security.What else can you do? Steer clear of words found in the dictionary, pronouns, usernames, and other predefined terms, as well as commonly used passwords – the top two in 2015 were “123456” and “password” (yes, you read that right). Also, never use the same password in different places (that forgotten account at a site you never use could lead to a bank account breach).
Force Brute Hacker Download
Consider using a password generator in order to get a complex password with no discernible pattern to help thwart password crackers. Finally, if memorizing long strings of characters proves too taxing, consider adopting a password manager that stores all your passwords. No password is perfect, but taking these steps can go a long way toward security and peace of mind.
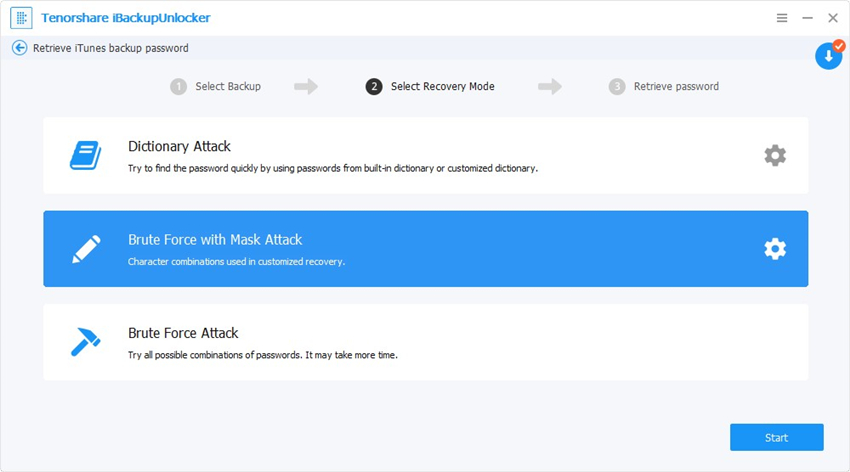
What are brute force login attacks and how can I protect my users and applications from them?A is one of the most common (and least subtle) attacks conducted against Web applications. The aim of a brute force attack is to gain access to user accounts by repeatedly trying to guess the password of a user or a group of users. If the Web application does not have any protections in place against this type of attack, it’s possible for automated tools - which are readily available on the Internet - to submit thousands of password attempts in a matter of seconds (or less), making it easy for an attacker to beat a password-based authentication system. Attacks can be conducted in a number of ways. If the length of the password is known, every single combination of numbers, letters and symbols can be tried until a match is found. However, this is a slow process, especially as the length of the password increases (which is why long passwords are better than short). The alternative is to use a list of common words, which is known as a dictionary attack.
A dictionary attack will generally try all English words, with the option of adding numbers or doubling up the word as the potential password. This has far fewer combinations, but still has a high chance of finding the correct password.Rather than trying many passwords against one user, another brute force attack method is to try one password against many usernames. This is known as a reverse brute force attack. This technique is worth noting as it is where most account lockout policies fail. Reverse brute force attacks are less common, however, because it’s often difficult for the attacker to compile a sufficiently large volume of usernames for the reverse attack.Preventing brute force attacksThere are a number of techniques for. The first is to implement an account lockout policy. For example, after three failed login attempts, the account is locked out until an administrator unlocks it.
The disadvantage of this method is that multiple accounts can be locked out by one malicious user, causing a denial of service for the victims and lots of work for the administrator.A better, albeit more complicated technique is progressive delays. With progressive delays, user accounts are locked out for a set period of time after a few failed login attempts.
The lock-out time increases with each subsequent failed attempt. This prevents automated tools from performing a brute force attack and effectively makes it impractical to perform such an attack.Another technique is to use a challenge-response test to prevent automated submissions of the login page. Tools such as the free can be used to require the user to enter a word or solve a simple math problem to ensure the user is, in fact, a person. This technique is effective, but has accessibility concerns and affects usability of the site.Any Web application should enforce the use of. At a minimum, requiring users to choose passwords of eight letters or more with some complexity (letters and numbers, or requiring one special character) is an excellent defence against brute force attacks when combined with one of the techniques outlined above.It may appear, at first, useful to use a tool that automatically reads Web logs and alerts an administrator if multiple attempts come from one IP address. However, it is fairly simple for an attacker to use a variety of tools to automatically and regularly change his or her IP address.It is important to ensure the Web application employs at least one of these techniques for defending against brute force attacks if your users are to trust the security of their personal data. Using the techniques outlined in this article should provide a against this common type of attack.
Brute Force Password Cracker
By submitting my Email address I confirm that I have read and accepted the Terms of Use andRelated Q&A fromThe OneOps cloud application lifecycle management tool helps organizations regain control of cloud deployments and prevent vendor lock-in. Expert Rob.Do your Web app users upload files to your servers? Find out the dangers of malicious file uploads and learn six steps to stop file-upload attacks.Forced browsing is when an attacker discovers the URL of a restricted webpage. Expert Rob Shapland explains how to halt this browser attack method.Read more on Identity and access management products.